Pay is a Solana Foundation project that frames a very specific problem in the agent economy: software agents can call APIs, but they still struggle to pay for APIs in a clean, user-authorized, machine-readable way. The repository describes Pay as a missing payment layer for HTTP, built to handle x402 and MPP payment challenges with stablecoin signing that remains under the user’s control.
That positioning matters because the next generation of software will not only browse, summarize, and generate. Agents will increasingly need to buy data, unlock endpoints, request computations, compare providers, and pay for small pieces of digital work at the moment they are needed. Pay is an attempt to make that interaction feel less like a subscription signup and more like a native part of the request-response cycle.
Why API payments become harder in an agent world
The traditional API economy was designed for human-run applications. A developer signs up for an account, stores an API key, chooses a plan, monitors usage, and periodically receives an invoice. That model works reasonably well for long-lived apps, internal integrations, and predictable workloads. It works less well when an AI agent needs to discover a service, make a small paid request, and continue its workflow without asking a human to create another account or paste another secret.
Agents turn API purchasing into a more dynamic problem. A human may subscribe to one weather API, one mapping API, one financial-data API, and one search API. An agent, however, may need to decide between many narrow providers in real time. It may need one paid call for a map route, another paid call for a market quote, another paid call for a document conversion, and another paid call for a specialist data source. The unit of purchase becomes smaller, more contextual, and more frequent.
The obvious workaround is to give the agent a collection of API keys. That is convenient, but it does not solve the trust problem. An API key is usually a broad credential: it can authorize many requests until revoked, often with limits that are enforced outside the moment of decision. For an agent workflow, that can create an awkward mismatch. The user may want the agent to spend a few cents on one request, but not to hold an open-ended credential that could be misused by a buggy tool, an unsafe prompt, or a compromised dependency.
Another workaround is central billing through a platform. In that pattern, the agent platform aggregates payments, brokers access to tools, and bills the user later. This can be practical, but it also concentrates power. The platform becomes the gatekeeper for what APIs are easy to buy, how providers are discovered, how spending is limited, and how much friction appears between a request and a result. For some categories, central billing will remain useful. For the broader web of machine-to-machine services, it risks reproducing the app-store problem: discovery and payment become easier, but only inside the walls of the intermediary.
A future-facing API payment layer needs a different shape. It should let an endpoint advertise that payment is required. It should let the client understand the payment challenge. It should let the user authorize a specific payment without exposing a private key or a permanent spending credential to the agent. And it should let the request continue once proof of payment exists. That is the gap Pay is trying to occupy.
What the Pay repository says it provides
The repository’s own description is compact: Pay handles x402 and MPP payment challenges with user-authorized stablecoin signing. In practical terms, it wraps selected command-line tools and watches for a paid API response. When a stablecoin-gated API returns an HTTP 402-style payment requirement, Pay detects the relevant protocol, prepares the transaction, asks the local wallet backend to authorize and sign it, and retries the request with payment proof.
That sequence is important. Pay is not presented as a replacement for APIs, and it is not merely a wallet. It sits between the caller and the paid endpoint, translating a payment challenge into a user-approved transaction and then back into a completed HTTP request. The payment becomes part of the API call’s lifecycle rather than a separate account-management task.
The project documentation highlights support for two live payment standards on Solana: MPP, the Machine Payments Protocol, and x402, the x402 Payment Protocol. It also states that stablecoins deployed to Solana are supported out of the box. Those details suggest that Pay is aimed at a world where agents do not simply hold balances inside a closed SaaS account. Instead, they interact with payment protocols that can be implemented by different services and settled through Solana-based stablecoin rails.
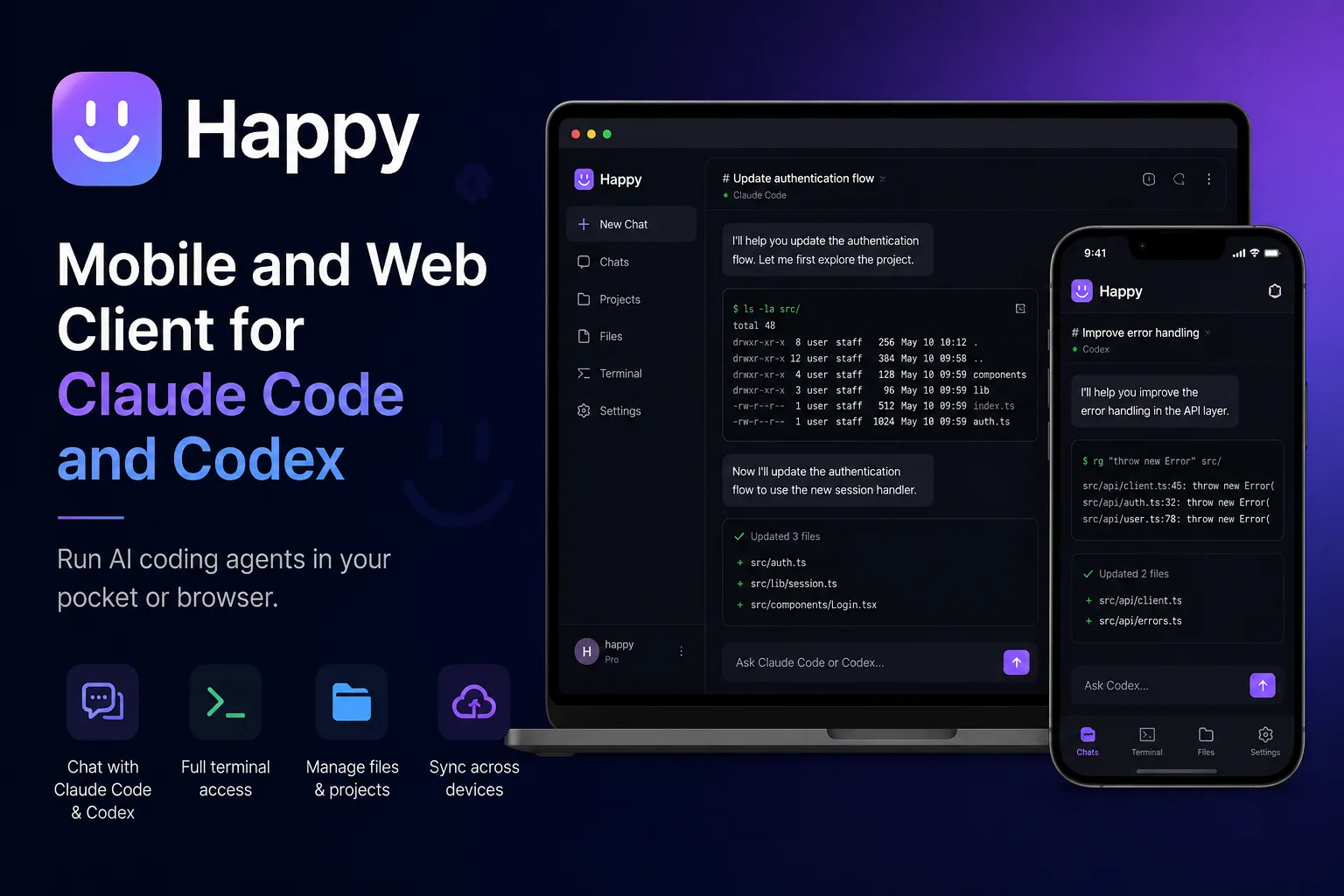
Pay also has an agent-specific angle through MCP. The README says it ships with a built-in MCP server, allowing AI assistants to request paid API calls through the same local wallet-approval flow. That makes the project more than a command-line convenience. MCP is increasingly used as a way to connect AI assistants to external tools, so adding payment authorization to that pattern addresses a concrete bottleneck: agents can be connected to tools, but the moment a tool requires payment, the workflow usually breaks.
The repository also describes an embedded Payment Debugger. According to the README, the debugger is a local web UI that visualizes every 402 challenge-response cycle as a sequence diagram, including the headers, the protocol used, and where things went wrong. That sounds like a small feature, but for payment infrastructure it matters. Developers need to understand not only whether a paid request succeeded, but also why it failed: Was the protocol unsupported? Did the wallet decline? Was proof attached incorrectly? Did the endpoint reject the payment? Debugging a payment flow as an HTTP exchange is much easier when the challenge, signature, proof, and retry can be inspected.
The project further describes gated payments through local authorization. It says Pay lets AI agents use paid APIs without giving them a private key or an API-wide spending credential. When a command, Claude Code, Codex, or another MCP client hits a paid endpoint, Pay prepares the payment locally and asks the wallet backend to authorize the signature. The README describes Touch ID through Keychain on macOS, Windows Hello on Windows, GNOME Keyring or polkit on Linux, and 1Password as an option. The basic security posture is therefore clear: the agent can ask for a paid action, but the local user authorization step decides whether money actually moves.
Finally, Pay is tied to an open source catalog concept. The README points to a pay-skills repository where paid API catalog entries can be contributed. It says entries can include provider listings, endpoint metadata, pricing, and usage guidance for agents. That is a crucial piece of the agent-payment puzzle. Payments alone are not enough. Agents also need to know which paid endpoints exist, how they are priced, what they are useful for, and what constraints apply before a request is made.
Why Solana is an interesting fit for this problem
The Pay repository is specifically built around Solana-based payment standards and stablecoin signing, so the Solana angle is not incidental. Solana Pay’s broader documentation describes Solana Pay as a standard protocol and set of reference implementations that help developers incorporate decentralized payments into apps and services. It also emphasizes fast confirmation and low average transaction cost. For agent API payments, those characteristics are not cosmetic. They are part of the economic design space.
API payments by agents may often be small. A single request to a specialized data provider might not justify a credit-card checkout, a subscription, or a monthly invoice. If each agent action needs a human-scale payment flow, the model fails. The payment rail needs to make small transactions feel operationally reasonable. It also needs to avoid turning every paid call into a slow detour that breaks the user’s workflow.
Stablecoins are also relevant because API providers usually want a predictable unit of account. A volatile token can be interesting for speculation, but it is inconvenient for pricing an endpoint that costs a fixed amount per call. Pay’s README does not claim to solve every stablecoin or pricing issue, but it does say stablecoins deployed to Solana are supported out of the box. That points to a practical idea: APIs can be priced in stable units while still using blockchain settlement and wallet authorization.
The bigger point is not that every API should use Solana. It is that agents need a payment method that is programmable, inspectable, and granular. Solana’s role here is to provide payment infrastructure that can be called at machine speed while still leaving a user-controlled signing step in place. Pay then packages that infrastructure in a way that developer tools and AI assistants can use.
There is also a standards question. If each provider invents its own payment prompt, wallet flow, metadata structure, and retry mechanism, agents will face the same fragmentation that humans already face with logins and subscription walls. Pay’s support for x402 and MPP is significant because it suggests a standards-based direction rather than a single proprietary checkout. In a mature agent economy, the winning pattern may not be one wallet, one blockchain, or one vendor. It may be a shared language for payment challenges, spending authorization, and proof.
The HTTP 402 status code has long been associated with payment required, but in much of the web it remained more of a placeholder than a widely used economic mechanism. Agentic software gives that idea a new practical reason to exist. A client that can understand a payment challenge, ask for authorization, and retry with proof could make 402-style flows useful in places where conventional checkout is too heavy.
Who this approach fits best
Pay is most relevant to developers who are already thinking about AI agents as active software clients rather than passive chat interfaces. If an agent is only summarizing documents or generating text from a fixed model subscription, payment orchestration may be unnecessary. But once an agent begins to choose external services, the question of how it pays becomes unavoidable.
The first likely audience is developers building agent runtimes, command-line workflows, or MCP-based tool environments. Pay’s README names command-line tools and MCP clients as part of its intended usage pattern. For those developers, Pay offers a way to explore paid API access without embedding payment logic directly into every tool. The agent can keep using a normal request workflow while Pay handles the payment challenge and proof exchange around it.
A second audience is API providers experimenting with pay-per-use access. Many providers dislike the friction of account creation for small requests. A user who wants one data point, one enrichment, one conversion, or one specialized lookup may not want to create yet another account. A payment-challenge model could let providers monetize narrow capabilities directly. The provider still needs to implement the gated endpoint and choose appropriate pricing, but the client side becomes more approachable if tools like Pay can handle the payment flow.
A third audience is developers who care about keeping authorization local. Giving an agent a private key would be reckless. Giving it an unlimited spending credential is also risky. Pay’s model, as described by the project, keeps the signing step behind a local wallet backend and platform-level approval method. That is not a complete governance system, but it is a meaningful distinction: the agent can trigger the request path, while the user or local wallet policy can still approve or reject payment.
A fourth audience is the catalog-builder community. The README’s mention of pay-skills suggests an ecosystem where paid APIs are discoverable in a structured format. That may be one of the hardest parts of the problem. Agents do not only need a payment button. They need reliable descriptions of endpoints, pricing, limitations, and recommended usage. Without that metadata layer, agents will either overpay, fail to understand provider differences, or depend on hard-coded integrations.
The fit is less obvious for organizations that require procurement controls, centralized invoicing, negotiated enterprise pricing, or strict vendor onboarding. Those needs do not disappear just because an agent can authorize a stablecoin payment. In many companies, API usage is a budget, compliance, and data-governance issue. Pay may still be interesting in internal experiments, but production adoption would likely need policy controls around budgets, audit trails, allowed providers, and approval rules.
Practical adoption notes for developers
A cautious way to evaluate Pay is to treat it as an interface experiment first and a payment dependency second. The core question is not simply whether a paid call succeeds. The more important question is whether the workflow feels safe: Can the user understand what the agent is trying to buy? Can they see the amount? Can they reject the payment? Can a developer debug failures? Can provider metadata be reviewed before use?
The README describes prebuilt installation options through Homebrew and npm, plus installation from source. It also describes setup and identity verification commands, a sandbox-style paid API call through debugger endpoints, and agent usage through Claude Code or Codex. A team exploring the project should start with the documented sandbox and debugger paths rather than connecting valuable accounts or important workflows immediately.
For an API provider, the adoption path begins on the server side. The endpoint needs to return a payment challenge in a protocol the client understands. Pay’s README names x402 and MPP as supported standards on Solana. The provider also needs to decide how much information to expose in the challenge, how to price the request, how to validate proof, and how to prevent abuse. A paid endpoint is still an API endpoint, so rate limiting, input validation, fraud controls, and observability remain necessary.
For an agent developer, the adoption path is more about tool boundaries. A good design would avoid giving the agent direct control over the wallet. The agent should formulate the intent and request the paid action. The local payment layer should prepare the transaction, present the authorization prompt, and enforce any budget or approval rules that exist. Pay’s local wallet-approval flow is aligned with that separation.
The debugging layer deserves special attention. Payment flows fail in more ways than normal API calls. A normal API failure may be a 404, a timeout, a bad key, or invalid input. A paid API call can additionally fail because the payment protocol was not recognized, the wallet could not sign, the user rejected authorization, the proof was malformed, the provider did not accept the settlement, or the retry path was not constructed correctly. The README’s description of a local debugger that visualizes challenge-response cycles directly addresses this complexity.
The catalog layer is equally practical. If agents are expected to choose paid APIs, provider metadata needs to be more than marketing copy. It should include endpoint capabilities, pricing structure, usage guidance, and limits in a format that both humans and agents can inspect. Pay’s linked catalog concept points in that direction, although real-world quality will depend on contribution standards, review, provider accuracy, and ongoing maintenance.
A strong production pattern would likely combine several layers: protocol-level payment challenges, local signing authorization, spending limits, allowlists of trusted providers, human-readable payment prompts, machine-readable endpoint metadata, and logs that connect a paid request to the user intent that triggered it. Pay does not need to solve every part alone, but it is useful because it makes the payment step explicit in the API interaction rather than hiding it inside credentials.
Caveats and open questions
The most important caveat is that agent payments are not just a technical problem. They are also a governance problem. A tool can ask for a wallet signature, but it cannot automatically decide what a user should consider worth buying. If agents begin to chain paid calls together, users will need clear spending controls. A single approval prompt may be enough for occasional use, but recurring autonomous work will require budgets, thresholds, provider policies, and auditability.
There is also a user-experience challenge. Payment prompts must be understandable at the exact moment of decision. If the prompt is too vague, users will approve blindly. If it is too noisy, users will reject useful workflows. The right prompt needs to show what is being purchased, from whom, for what amount, and why the agent believes it is necessary. The README describes local authorization mechanisms, but the broader UX discipline around agent spending is still emerging.
Provider adoption is another open question. Pay can wrap clients and support protocols, but paid API infrastructure only becomes valuable if providers expose useful endpoints through compatible payment challenges. The open catalog idea helps, yet catalogs are only as good as their coverage and maintenance. A small number of demos can prove the concept; a deep marketplace of reliable paid APIs would be a larger ecosystem effort.
Regulatory and accounting concerns may also matter. Stablecoin payments can be attractive for small digital purchases, but businesses still need records, invoices, tax treatment, refund policies, and compliance workflows. Those needs differ by jurisdiction and use case. A developer experimenting with a paid endpoint may not care at first, but a company deploying autonomous paid agents at scale will care very much.
Security remains central. Pay’s README emphasizes that agents should not receive the user’s private key or an API-wide spending credential. That is the right starting point. Still, any local signing flow needs careful handling of malware risk, prompt injection, compromised tools, confusing authorization screens, and dependency vulnerabilities. A safe architecture should assume that an agent may be mistaken, manipulated, or overconfident. Payment approval should remain bounded and inspectable.
There is also the question of when blockchain settlement is the right answer. For some API markets, conventional invoicing, prepaid credits, or platform billing will remain simpler. Pay is most compelling where the purchase is small, the provider relationship is lightweight, the agent needs real-time access, and direct programmable payment is valuable. It is less compelling where procurement, contractual service levels, or private enterprise pricing dominate the relationship.
Finally, the project should be read as an evolving developer tool, not as proof that the future API economy has already settled on one architecture. The repository is open source under an MIT license, according to its license file, and the README welcomes contributions. That openness is valuable, but it also means developers should inspect the code, review the security model, test with small amounts, and follow the project’s documentation before building critical workflows around it.
Editorial verdict
Pay is interesting because it addresses a problem that will become more visible as agents move from text generation into action. A useful agent cannot live entirely inside a chat box. It will need to call services, unlock data, and sometimes pay for resources that are too narrow or temporary for a subscription. The old API-key model was built for developers and applications. The next model needs to work for agents acting under user authority.
The Solana Foundation’s Pay project proposes a pragmatic shape for that future: HTTP payment challenges, Solana-based stablecoin settlement, local wallet authorization, MCP support for agent workflows, debugging tools for developers, and an open catalog direction for paid API discovery. None of those pieces alone solves the full economic, governance, and UX problem. Together, they form a credible experiment in making API payments agent-native.
The strongest idea is not simply that agents can spend money. The stronger idea is that they should spend money without being handed dangerous credentials. Pay’s local approval flow keeps the payment boundary visible. The agent can request a paid call, but the wallet backend and user authorization decide whether the transaction is signed. That separation is likely to be essential if autonomous tools are going to interact with real markets.
The project is still best approached with care. Developers should treat paid agent calls as a high-trust workflow, even when the amounts are small. They should test the debugger, inspect the protocol flow, understand how signing is authorized on their platform, and think carefully about limits before allowing an agent to trigger payments repeatedly. API providers should be equally cautious about metadata quality, pricing clarity, and failure handling.
As an editorial signal, Pay is worth watching less because it claims to have every answer and more because it asks the right question: when agents become customers of APIs, what should payment look like? Solana’s answer here is a standards-oriented, stablecoin-based, user-authorized payment layer around HTTP. Whether that becomes a mainstream pattern will depend on provider adoption, wallet UX, policy controls, and developer trust. But the direction is clear: the future of APIs may not be only about keys and quotas. It may also be about agents making small, explicit, authorized purchases at the edge of each request.
Primary link
Learn more at: https://github.com/solana-foundation/pay